Employee online monitoring is a practice that involves overseeing employees’ use of digital technologies in the workplace in order to assess productivity, ensure security, and enforce company policies.
This typically includes tracking the websites employees visit, the emails they send and receive, and the software they use.
Online Monitoring Systems Are Becoming More and More Popular
Gartner VP Brian Knopp mentioned that over 50% of companies with over $750m annual revenue explored unconventional methods for monitoring employees.
These businesses monitor employee computer activity, including Internet, email, and phone usage. Some companies even track sleep patterns and heart rates to analyze how these factors affect their employees’ performance.
Typically, organization-level monitoring features can include tracking email client activity, app connectivity, authentication success rates, and mail flow, providing a comprehensive overview for the entire organization.
In 2017, Crowd Research Partners surveyed 472 cybersecurity professionals. The context of monitoring desktops revealed that:
- 94% of companies use some method of corporate surveillance
- 93% of organizations track access to sensitive data.
- 44% manage user behavior by employing online monitoring methods
Types of Online Monitoring
Online monitoring encompasses a variety of approaches, each tailored to different aspects of a business’s digital presence. The most common types include website monitoring, application monitoring, and network monitoring.
- Website Monitoring focuses on tracking the performance and availability of websites. It measures critical metrics like page load times, uptime, and error rates, ensuring that customers can access the site without interruption. This type of monitoring helps businesses quickly identify and resolve issues that could impact user experience or revenue.
- Application Monitoring is centered on the health and performance of software applications. It tracks metrics such as response times, user engagement, and error occurrences, providing insights into how applications are functioning in real time. This enables teams to detect and address issues before they escalate, maintaining a seamless experience for users.
For instance, a European healthcare software provider partnered with ScienceSoft to implement real-time application and network monitoring for its mobile app servers. By tracking server availability, performance, and network health, the team identified and resolved issues before they reached end users. - Network Monitoring involves keeping an eye on the performance and stability of a company’s network infrastructure. This process often includes supervising the traffic and encrypted tunnels managed by a virtual private network gateway. By tracking bandwidth usage, packet loss, and other network health indicators, businesses can prevent bottlenecks and security threats that might disrupt operations.
These monitoring tools collect and analyze data in real time, allowing organizations to respond swiftly to incidents and optimize their systems. By understanding user behavior, system performance, and potential security threats, businesses can make informed, data-driven decisions that enhance customer experience and drive continuous improvement.
Where Can You Use a Computer Monitoring System?

Remote computer monitoring comes in various forms. Here are the most common ways companies use this system:
- Web Activity – Under this category, a manager can monitor which URLs their team members open. It helps determine if an employee is doing their work or visiting online shopping sites, watching online videos, or even gambling in casinos. This category also covers URL blocking to prevent workers from accessing inappropriate content.
- Email – Monitoring emails can help settle disputes and identify data theft in a company. It also allows companies to spot risks and issues at their early signs. In most cases, it is legal for employers to investigate work emails in extraordinary circumstances like sexual harassment claims.
- Phone – Organizations can also record their staff’s phone communication with prospects, users, clients, and suppliers. It is beneficial in tracking support and performance statistics. This is also the reason why you mostly hear the default script, “This message may be recorded for quality assurance,” whenever you contact support numbers.
- Location – Certain industries use monitoring apps with GPS tracking to ensure the safety of their workforce. This monitoring method applies to delivery services, manufacturing settings, and construction sites.
- Other – There are other ways companies can monitor their employees’ activity. For instance, Buffer employees get a Jawbone UP wristband. This device tracks a user’s nutritional choices, exercise, and sleep. Results are transmitted online and are open to the entire company.
Online monitoring of employees is legally justified. However, as with any online monitoring software, it can be used for abusing workers.

There are undeniable concerns about ethics in online employee monitoring. However, it is perfectly justifiable as long as it is carried out without malicious intent. Managers can track an employee’s screen to ensure productivity and to protect against insider threats.
Ensuring Remote Workforce Productivity
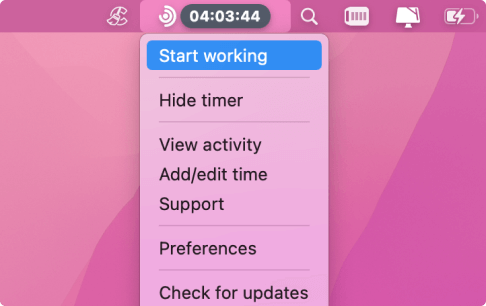
Organizations turn to online employee monitoring software to identify the applications used, break duration, attendance, and policy compliance. The data gathered by the tool gives managers an overview of the typical behavior of a remote worker. Consequently, it can be used to determine weaknesses, strengths, and productivity leaks. Time trackers give employers insight into the following:
- Time spent on applications tagged as non-productive/productive
- Faulty workflow and systems that may hinder productivity
- Quality of customer service
When employing a monitoring tool, it is crucial to have the ability to customize tracking according to user groups. One application may be considered useful for one role, yet it may not be beneficial for another. Take social media managers as an example. They spend most of their time working on ad campaigns for social networking sites like Twitter, Facebook, and Instagram. These platforms are an integral part of their job function.
Now, if these social media sites do not add value to the work of your remote employees, then seeing them in the tracking results can raise a red flag.
Protection Against Data Breaches
Your company’s sensitive data, network infrastructure, and intellectual property can be vulnerable to risks. Insiders like vendors, employees, and partners can become threats that will leak your data. There are two types of insider threats:
- Those with vengeful intent or nefarious motives of using critical information for financial gain
- Those with negligent behavior that is susceptible to scams
The 2017 Data Breach Investigations Report by Verizon revealed that 25% of the breaches they analyzed were caused by internal culprits.Part of the leakers were found to have malicious intent while a percentage were found to be negligent insiders. Another 2% of the factors behind the breaches were credited to another type of insider threat—partners.
The thing is, end users find convenient ways to improve efficiency. Because companies want bigger results in a shorter amount of time, employees resort to dangerous workarounds. Intermedia Cloud Communications’ 2017 Data Vulnerability Report provides an insight into this practice. After surveying on over a thousand employees, they discovered that:
- 99% of the employees have committed at least a single, potentially dangerous action. This includes storing and sharing login credentials, as well as transmitting work files to personal email accounts.
- 34% have admitted to using sync-and-share services to store work documents. Doing so allowed them to access the saved files even after leaving office premises, using their personal accounts.
Traditional security systems are usually not focused around the aforementioned perimeters. As such, they fail to spot insider threats and attacks before or as they happen within the network. A failure to detect insider threats or data compromise can result in significant security incidents, making robust monitoring essential to prevent such failures. Now, managers are asking themselves, “What is a way of monitoring the entire system in a company?” With that in mind, they use tracking tools that will offer insightinto online activities across crucial IT systems.
Online monitoring software can help managers understand the typical activity patterns around file transfers, instant messages, emails, and external storage use. The system identifies red flags that can be considered as data compromisers and insider threats. In some cases, organizations can also use these tools to actively block these potentially dangerous activities.
Implementation and Best Practices
Successfully implementing a monitoring tool requires a strategic approach and adherence to best practices. Start by customizing alerts and notifications so that the right team members are informed of issues as soon as they arise. This ensures a rapid response to incidents and minimizes potential downtime.
Integrating monitoring tools with other business systems—such as incident management and project management software—streamlines workflows and improves overall efficiency. It’s also important to establish clear objectives for your monitoring efforts, whether your focus is on improving customer experience, reducing downtime, or strengthening security.
Track key performance indicators (KPIs) and other relevant metrics to measure progress toward your goals. Regularly review and analyze monitoring data to identify trends, uncover root causes of recurring issues, and spot opportunities for optimization. Providing actionable insights and feedback to developers and IT teams helps them fine-tune applications and enhance performance.
By following these best practices and making the most of your monitoring tools, your business can boost performance, strengthen security, and deliver a superior customer experience. Continuous monitoring and improvement are key to staying ahead in today’s fast-paced digital landscape.